Important international standards at a glance


Standards are the concentrated expertise of people who have deep knowledge in their industry and understand the requirements of the organizations they represent: manufacturers, suppliers, clients, users, professional associations, and authorities. Based on this shared wealth of experience, norms and requirements are created that help to work more systematically and successfully.

Discover some of the best-known and most widely used standards, as well as those that address current challenges and changes that affect us all.
Information security, cybersecurity and privacy protection – Information security controls
(Information security, cybersecurity and privacy protection – Information security controls)
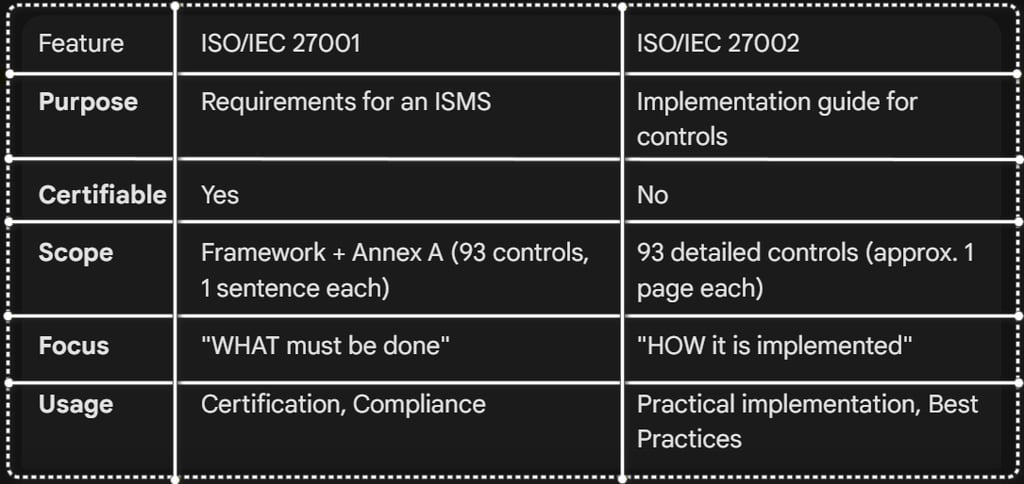
ISO/IEC 27002:2022 is the implementation guide for information security controls. While ISO/IEC 27001 defines the requirements for an ISMS and only briefly describes which controls exist (Annex A), ISO/IEC 27002 goes into depth and explains how each individual control can be practically implemented.
The fundamental difference:
ISO/IEC 27001 says: "You must implement access control" (1 sentence in Annex A).
ISO/IEC 27002 says: "How to implement access control: Purpose, procedure, technical details, best practices, typical mistakes" (1 full page).
ISO/IEC 27002:2022 is not certifiable – it is a reference document that you use together with ISO/IEC 27001 to successfully build your ISMS. It informs organizations exactly what each control means, why it is important, and how it should be concretely implemented.
Structure of ISO/IEC 27002:2022: The standard describes 93 security controls, grouped into 4 categories (themes):
Organizational controls (37 controls) – Governance, policies, risk management, supplier management.
People controls (8 controls) – Training, background checks, awareness.
Physical controls (14 controls) – Building security, access controls, protection against environmental threats.
Technological controls (34 controls) – Access control, encryption, network security, secure software development.
Each control in ISO/IEC 27002:2022 contains:
Purpose: Why is this control important?
Description: What does the control involve?
Implementation guidance: How do you implement it?
Other information: Additional notes, best practices.
Attribute System: ISO/IEC 27002:2022 introduces an innovative attribute system that categorizes each control according to several dimensions:
Control type: Preventive, Detective, Corrective.
Information security properties: Confidentiality, Integrity, Availability.
Cybersecurity concepts: Identify, Protect, Detect, Respond, Recover (aligned with NIST).
Operational capabilities: Governance, Asset Management, Identity Management, etc.
Security domains: Governance, Protection, Defense, Resilience.
These attributes help organizations filter controls according to their specific needs and link them with other frameworks (NIST, CIS Controls).
What is ISO/IEC 27002:2022?
Why is ISO/IEC 27002:2022 important?
ISO/IEC 27001 alone can be overwhelming: "Implement 93 controls" – but how exactly? This is where ISO/IEC 27002 comes into play. It is the bridge builder between theory and practice.
Without ISO/IEC 27002:
Organizations have to guess how controls should be implemented.
Different interpretations lead to inconsistent implementations.
Auditors find gaps because best practices were not observed.
With ISO/IEC 27002:
Clear, practical instructions for each control.
Uniform understanding across the entire team.
Higher success rate in audits and certifications.
Particularly valuable for:
Security teams, who need concrete implementation steps.
IT departments, which implement the technical controls.
Consultants and auditors, who need to interpret the standards consistently.
Management, which wants to understand why certain controls are important.
Benefits for Your Business
Practical Implementation instead of Theory
ISO/IEC 27002 transforms abstract requirements into concrete instructions for action. You know exactly what needs to be done — no guesswork.
Faster Implementation
With clear instructions and best practices, the time to full ISMS implementation is significantly reduced. Teams can start immediately without having to hire external consultants first.
Higher Audit Success Rate
Organizations that use ISO/IEC 27002 as a guide pass audits more often on the first attempt because they know what auditors expect.
Consistent Implementation throughout the Company
All departments work according to the same standards and best practices — no more conflicting interpretations.
Better Security Culture
Detailed explanations help employees understand why certain measures are important, which leads to a higher level of engagement.
Cost Savings
Through structured implementation, expensive mistakes are avoided. You invest specifically in the right controls instead of wasting budget on ineffective measures.
Preparation for Modern Threats
The 11 new controls address current risks such as cloud security, ransomware, and supply chain attacks — your ISMS stays up to date.
Compatibility with Other Frameworks
The attribute system allows for easy linking with the NIST Cybersecurity Framework, CIS Controls, and other standards.
Summary of the Most Important Benefits
Clear, practical implementation instructions for all 93 controls
Faster and more efficient ISMS implementation
Higher success rate in audits and certifications
Consistent implementation throughout the company
Better understanding and higher acceptance among employees
Cost savings through targeted investments
Coverage of modern threats (Cloud, Ransomware, Supply Chain)
Compatibility with NIST, CIS Controls, and other frameworks
For whom is ISO/IEC 27002:2022 relevant?
ISO/IEC 27002:2022 is relevant for everyone who implements ISO/IEC 27001 or already operates an ISMS:
Security Teams and CISOs (Concrete implementation steps for 93 controls)
IT Departments (Technical implementation instructions)
Compliance and Risk Managers (Understanding of control objectives)
Consultants and Auditors (Standardized interpretations)
Management and Executive Board (Basis for investment decisions)
Online Academies and E-Learning Platforms (Protection of learner data)
SaaS and Cloud Architects (Cloud security controls)
E-Commerce and Online Service Providers (Payment data security)
Small and Medium-sized Enterprises (Structured security implementation)
How does EAS™ support you with ISO/IEC 27002:2022?
A.5 Organizational Controls (37 controls)
These controls concern governance, policies, processes, and organizational framework conditions:
Important Controls:
A.5.1 Policies for information security — Creation and communication of security guidelines
A.5.7 Threat Intelligence — Collection and analysis of threat information
A.5.9 Inventory of information and other associated assets — Asset Management
A.5.19 Information security in supplier relationships — Security with third parties
A.5.23 Information security for cloud services — Cloud Security
A.5.24 Incident Management — Planning and response to security incidents
A.5.30 ICT readiness for business continuity — IT contingency plans
A.6 People Controls (8 controls)
These controls concern people and their role in information security:
Important Controls:
A.6.1 Screening — Background checks upon hiring
A.6.2 Employment contracts — Security clauses in contracts
A.6.3 Awareness, education and training — Continuous education
A.6.4 Disciplinary process — Dealing with security violations
A.6.5 Responsibilities after termination — Offboarding processes
A.6.8 Remote Work — Security in the home office and mobile work
A.7 Physical Controls (14 controls)
These controls concern the physical security of buildings, rooms, and devices:
Important Controls:
A.7.1 Physical security perimeters — Demarcation and protection of sensitive areas
A.7.2 Physical entry — Access controls to buildings and rooms
A.7.4 Physical security monitoring — Surveillance cameras, alarms
A.7.7 Clear Desk and Clear Screen — Clean desks and screens
A.7.10 Secure disposal or re-use of devices — Deletion of data
A.8 Technological Controls (34 controls)
These controls concern IT systems, networks, applications, and data:
Important Controls:
A.8.1 User end point devices — Security of laptops, smartphones
A.8.2 Privileged access rights — Management of admin rights
A.8.3 Information access restriction — Need-to-know principle
A.8.5 Secure authentication — Passwords, multi-factor authentication
A.8.9 Configuration management — Management of system configurations
A.8.10 Information deletion — Secure data deletion
A.8.11 Data masking — Protection of sensitive data in test environments
A.8.12 Data leakage prevention — Data Loss Prevention (DLP)
A.8.16 Monitoring activities — Logging and Monitoring
A.8.23 Web filtering — Control of internet access
A.8.24 Use of cryptography — Encryption
A.8.26 Application security requirements — Secure Development
A.8.28 Secure coding — Secure Coding Practices
A.8.31 Separation of development, test and production environments
_______________________________________
📌 Learn more: Visit the ISO website or contact an EAS™-certified auditor for a comprehensive consultation on your specific situation.




The 4 Categories of ISO/IEC 27002:2022 in Detail
The European Attestation Standard™ (EAS™) is based on the practical controls of ISO/IEC 27002:2022 and ensures that your online services and digital offerings are protected according to the same best practices — without you necessarily having to be ISO-certified yourself.
By using EAS™ criteria, you can:
Implement concrete security controls according to ISO standards
Structure your technical, organizational, and personnel measures
Apply best practices for cloud security, access control, and data protection
Prepare your organization for a future ISO/IEC 27001 certification
Build trust among learners, customers, and partners through demonstrable security
Communicate professionally with auditors, regulatory authorities, and enterprise customers
What has changed in ISO/IEC 27002:2022?
The 2022 version is a fundamental revision of the previous 2013 version.
From 114 to 93 controls:
58 controls were updated and modernized.
24 controls were created by merging 57 older controls (consolidation).
11 new controls were added to address modern threats.
From 14 domains to 4 categories:
Old structure: 14 domains (Asset Management, Access Control, Cryptography, etc.).
New structure: 4 clear categories (Organizational, People, Physical, Technological).
The 11 new controls in ISO/IEC 27002:2022:
A.5.7 Threat intelligence – Proactive collection and analysis of threat information.
A.5.23 Information security for cloud services – Security in cloud environments.
A.5.30 ICT readiness for business continuity – Contingency plans for IT systems.
A.7.4 Physical security monitoring – Surveillance of buildings and rooms.
A.8.9 Configuration management – Management of system and software configurations.
A.8.10 Information deletion – Secure deletion of data.
A.8.11 Data masking – Protection of sensitive data in test and development environments.
A.8.12 Data leakage prevention – Technologies against data loss.
A.8.16 Monitoring activities – Monitoring of user and system activities.
A.8.23 Web filtering – Control of internet access.
A.8.28 Secure coding – Best practices for secure software development.
These new controls reflect the reality of modern IT environments: Cloud Computing, Remote Work, DevOps, Supply Chain attacks, and Zero Trust architecture.
ISO/IEC 27001 vs. ISO/IEC 27002: The Difference
Both standards are used together: ISO/IEC 27001 provides the structure, while ISO/IEC 27002 provides the details.
CONTACTS


Moosbach,
Germany, 92709
ADDRESS
© 2026 European Attestation Standard (EAS). All rights reserved.
FOR OUR INTERNATIONAL PARTNERS:
Our website is available in German, Ukrainian, English, and Italian. To support our cooperation, we provide official EAS documents and attestation materials upon request, not only in these languages but also in any other required language by agreement.